If you don’t where it is, you can’t protect it.
Do you know where ALL your organisation’s data is – not physically, but on which web and cloud services?
Here’s the problem. If you don’t where it is, then you can’t protect it. The secondary problem is finding out, because not everyone in your organisation will be onboard. It is common for people to sign up to web services because they offer something useful that helps them do their job.
They sign up using their email address and creating a password. There is the first headache – how does anyone track what has been signed up to across your organisation, let alone who has access to it? If that person leaves, no one will change the account credentials if they don’t know about it, but your ex-colleague still has access.
Secondly, what data do they upload? Is that data that you have a legal or moral responsibility for?
There’s nothing noble about Nobelium.
This isn’t theory – it’s real. USAID is a pretty important US organisation – promoting democracy and human rights around the world. Turns out, someone there was using a well-known email database tool called Constant Contact. But their account wasn’t well protected. Worse still, their account had a huge mailing set up, and of course, it had all the official USAID templates.
So, these Nobelium people, allegedly a Russian state-sponsored hacker group, compromised the Constant Contact account and sent a bulletin out. The bulletin contained malware that allowed the hackers to take command and control over victims computers. Ironically the fake email alleged interference in the US federal elections.

So, what can you do?
The first step is knowing what SaaS tools your people are using. We call this SHADOW IT and it is inevitable. Rather than stopping it, the job IT has is to identify it and manage it. The second step is to secure those platforms. That’s why our KARE for Security S2 plan contains a useful tool to help you identify what services your people are using.
Refer : What We Know About The Apparent Russian Hack Exploiting USAID : NPR
South Pacific Pictures – Case Study
"Working with Kinetics has helped us align our IT systems with the businesses need for streamlined systems and business continuity, as well as the comfort of compliance and reassurance from an industry specialist." - Kelly Martin, CEO, South Pacific Pictures...
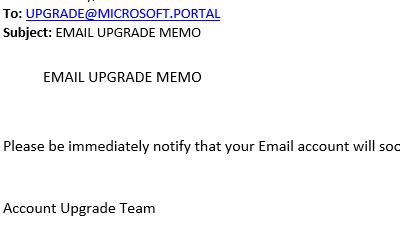
Beware (again) – The Phishermen are after you.
The deluge of clever phishing emails continues. This one caught our eye, because it looks so authentic. Given that we look after Office 365 for this customer, it left us wondering how we'd have missed 'verifying' their account. Well, only a for a moment! When we...
Clever iOS app scams
[header2 text="Scammers are getting smarter" align="left" color="#336A40" margintop=""] You could be forgiven for being overconfident about Apple's vetting of iOS apps. But you shouldn't be lulled into thinking that all iOS apps are safe - here is an example of an...
FAKE Microsoft 365 Renewal
Another day, another scam. One of our clients forwarded this little number to us today You can see that the link to 'microsoft' is spelt wrong, with one letter missing. If you are busy, you might miss it, and by telling you your email access is about to be...
The Spectre of a Meltdown
The Spectre of a Meltdown - 2018 starts with a security headache. Unhappily, our New Year starts by warning you about yet more security vulnerabilities. Whoever names these must have a lot of fun! Spectre and Meltdown are the latest, and these two effect virtually...
Christmas 2017
Its Christmas time again and the signs are its going to be great summer. No matter how good the weather is, we know that many of us need to keep in touch with our clients and our business. [header2 text="Our Hours" align="left" color="#3ec940" margintop=""] Kinetics...
4 Reasons IT training SUCKS!
[header2 text="1. Theory with no relevance" align="left" color="#336A40" margintop=""] No matter how amazing a training course is, how effective the trainer is and how much was learnt on the day, if the learning isn't applied back at your desk, you quickly...
KRACK Wireless Access Vulnerability
[header2 text="KRACK - Wireless Access Vulnerability" align="left" color="#336A40" margintop=""] It’s been all over the news that the dastardly hackers have struck again, this time hitting your favourite wireless. According to some reports, the world will end...
Another Scammer example
[header2 text="Not the worst we've seen, but equally effective" align="left" color="#336A40" margintop=""] The scammers never stop. This latest attempt is extremely poorly written. But when you follow the link it's a passable representation of the Office 365...
Giving clients better response times
[header2 text="Speeding up our service" align="left" color="#336A40" margintop=""] To speed up our service, we’ve introduced a new ‘ticket’ (job) logging system. This is in additional option to ringing us or emailing our ‘support’ email team. Each of these systems...