If you don’t where it is, you can’t protect it.
Do you know where ALL your organisation’s data is – not physically, but on which web and cloud services?
Here’s the problem. If you don’t where it is, then you can’t protect it. The secondary problem is finding out, because not everyone in your organisation will be onboard. It is common for people to sign up to web services because they offer something useful that helps them do their job.
They sign up using their email address and creating a password. There is the first headache – how does anyone track what has been signed up to across your organisation, let alone who has access to it? If that person leaves, no one will change the account credentials if they don’t know about it, but your ex-colleague still has access.
Secondly, what data do they upload? Is that data that you have a legal or moral responsibility for?
There’s nothing noble about Nobelium.
This isn’t theory – it’s real. USAID is a pretty important US organisation – promoting democracy and human rights around the world. Turns out, someone there was using a well-known email database tool called Constant Contact. But their account wasn’t well protected. Worse still, their account had a huge mailing set up, and of course, it had all the official USAID templates.
So, these Nobelium people, allegedly a Russian state-sponsored hacker group, compromised the Constant Contact account and sent a bulletin out. The bulletin contained malware that allowed the hackers to take command and control over victims computers. Ironically the fake email alleged interference in the US federal elections.

So, what can you do?
The first step is knowing what SaaS tools your people are using. We call this SHADOW IT and it is inevitable. Rather than stopping it, the job IT has is to identify it and manage it. The second step is to secure those platforms. That’s why our KARE for Security S2 plan contains a useful tool to help you identify what services your people are using.
Refer : What We Know About The Apparent Russian Hack Exploiting USAID : NPR
MS OFFICE ZERO DAY ATTACK – MAY 31st
One of the scariest news items to wake up to is that there is a ‘zero-day’ vulnerability in a common piece of software. That means that the hacking community has found an opportunity to hack a bit of software and there is no update yet – ‘zero’ days to apply a fix....
Beware – When Anti-Money Laundering (AML) CREATES a risk
That’s right. AML is not only frustrating to many of us, but it has also created cyber-risks. The irony isn’t lost on us. We’re honoured to support a large number of NZ law firms as clients, and it is a responsibility we take very seriously. Law firms handle such a...
Get some Viva Inspiration
Viva Insights has given us the opportunity to say how we’re feeling, protect our time and even meditate. It now has a new feature - currently in preview mode - that lets you draw on a library of articles to inspire you. Drumroll please - it is called Inspiration...
Subject Lines in Teams Posts
Teams is great for sharing information by posting it to a Channel. However, a lot of the rich content we create becomes lost and is difficult to find based on the appearance as well as the quantity. To make things easier you can search. However maybe a bit more...
Is MFA driving you mad?
Getting tired of having to open your phone for access? If so, you are not alone! But, its necessary. Hackers are counting on you suffering from an excess of having to reach for your phone to approve access, with something called “MFA Fatigue Attacks”.MFA Fatigue...
Why have Microsoft changed the look of Outlook?
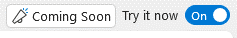
Depending on whether you have hit ‘coming soon’, you might have noticed that the navigation bar in Outlook has moved to the top left. This has sparked quite a lot of frustration amongst users, some of whom have added customised shortcuts to lists to the navigation...
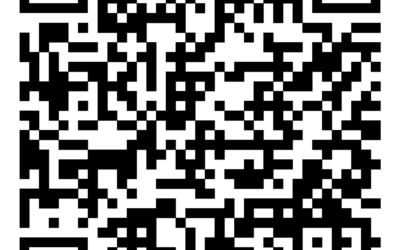
When QR codes go bad
Thanks to Covid, we’re all familiar with QR codes. Of course, with Covid, we were using the official tracer app to scan them, but in normal use, you can just use your phone’s camera to open the link. It’s a great way to make it easy to visit a website without having...
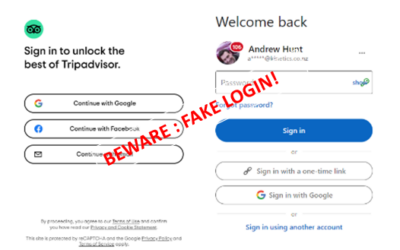
Is nothing safe? Fake logins!
Every day, there is a new cyber-threat to watch out for, and to warn friends and colleagues about. I’m frequently stunned when talking to friends and colleagues that these threats are abstract and academic. For the sake of absolute clarity, these cyber risks...
What is Kinetics ITMAAS? Customer Stories.
IT is critical to the operation of almost every organisation. If your IT is more than computers and mobiles then WATCH THIS WEBINAR. If IT is a critical asset to your organisation, then WATCH THIS WEBINAR. If what IT does matters more than what IT is, then WATCH THIS...
What? An update to Windows 11 already?
We’ve previously posted about Windows 11. You won’t believe it, but there is an updated version to it, already! There are over a billion Windows 10 users, and many of those can’t upgrade to 11 simply because their current machines don’t have the horsepower, but that’s...