If you don’t where it is, you can’t protect it.
Do you know where ALL your organisation’s data is – not physically, but on which web and cloud services?
Here’s the problem. If you don’t where it is, then you can’t protect it. The secondary problem is finding out, because not everyone in your organisation will be onboard. It is common for people to sign up to web services because they offer something useful that helps them do their job.
They sign up using their email address and creating a password. There is the first headache – how does anyone track what has been signed up to across your organisation, let alone who has access to it? If that person leaves, no one will change the account credentials if they don’t know about it, but your ex-colleague still has access.
Secondly, what data do they upload? Is that data that you have a legal or moral responsibility for?
There’s nothing noble about Nobelium.
This isn’t theory – it’s real. USAID is a pretty important US organisation – promoting democracy and human rights around the world. Turns out, someone there was using a well-known email database tool called Constant Contact. But their account wasn’t well protected. Worse still, their account had a huge mailing set up, and of course, it had all the official USAID templates.
So, these Nobelium people, allegedly a Russian state-sponsored hacker group, compromised the Constant Contact account and sent a bulletin out. The bulletin contained malware that allowed the hackers to take command and control over victims computers. Ironically the fake email alleged interference in the US federal elections.

So, what can you do?
The first step is knowing what SaaS tools your people are using. We call this SHADOW IT and it is inevitable. Rather than stopping it, the job IT has is to identify it and manage it. The second step is to secure those platforms. That’s why our KARE for Security S2 plan contains a useful tool to help you identify what services your people are using.
Refer : What We Know About The Apparent Russian Hack Exploiting USAID : NPR
Experience Virtual Reality today – available NOW in your Microsoft Teams
A curious little update appeared in Microsoft Teams recently, with very little fanfare. Have you noticed the “3D Immersive Experience” ? It’s called “Microsoft Mesh” It seems this is available through a range of interfaces, but the one we are interested in is Teams,...
Is MFA enough? – the need for multiple cyber security layers.
At Kinetics, we've always emphasized the importance of multi-factor authentication (MFA) as a critical layer in cybersecurity. Without MFA, it's only a matter of time before you fall victim to a cyber attack. However, as we've also mentioned, no single defense is...
Securing your Mac
It does not seem that long ago I would hear Mac users say “I don’t need Anti-Virus”, or "Mac’s are not affected". To a certain extent they were right. Apple's use of tightly controlled application approvals reduced the surface area for attack. Mac users did not enjoy...
How secure is your cloud IT? Is it as safe as you expect?
Your cloud computing can be safe and secure, or open and vulnerable - the choice is yours. With the rise of hacker activity and cybercrime, it’s essential to lock down your cloud and protect it from threats. For most businesses, the standard 365 settings aren't...
What would you do Canterbury? Incident Response Workshop
Mastering Cybersecurity What would you do? Table-top exercise Join us for an interactive table-top simulation exercise. Imagine - you are busy going about your day when suddenly your meeting is interrupted. "No one can access their files" or "We just accidently paid...
Webinar Replay: AVD – the future of secure remote access to non-365/web-based software
In this cloud world, are virtual desktops still relevant? How can work-from-anywhere be MORE flexible, easy and cost-effective?This webinar replay is a must-watch if want: To cost-effectively add cyber-security for remote workers on personal devices Easily access...
Have you met Microsoft Loop?
Have you noticed the Microsoft Loop icon in your 365 screen? (It's been there for a few months) Loop is a comparatively new collaborative app that allows users to create, share, and work together on various types of content, including notes, tables, lists, and more....
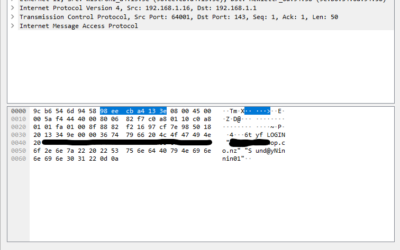
Are your legacy IT systems giving hackers a backdoor into your business?
One of our engineers was working on migrating a customer from a legacy email server into Office 365 after we discovered they were under a brute force external attack. The migration required that we receive the users passwords. These would, of course, be reset after...
Empower your non-profit with the latest Microsoft Technology, including Co-Pilot (Auckland)
Empower your non-profit with the latest Microsoft TechnologyThis in-person Masterclass will highlight Microsoft's "Tech for Social Impact" initiative that aims to accelerate digital transformation across the Not-for-Profit/For-Purpose sector globally, so they can have...
Is your Teams calling giving the actionable data you need?
Like many businesses, we rely on Microsoft Teams for our messaging and voice/video calling It's easy to use, works well on all our devices and is highly reliable. But the standard reporting wasn't working for us. We were completely frustrated We knew our...