Free IT Training Events: Expert Webinars & Workshops
To keep you informed.
Upcoming Live IT Training Events
AI Innovation Circle (Free)
Join other business managers in an honest, collaborative exploration of AI. No sales pitches. No unrealistic promises. Just real businesses sharing their genuine experiences, challenges, and solutions.
NExt Session – Thursday, 26 March 2026
Story circle format where participants share their AI journey so far, address myths and fears, and form exploration partnerships. Focus on honest discussion about what AI actually means for small businesses.
(Free) Webinar – Beyond Antivirus: Understanding MDR and ITDR for Modern Cyber Defence
Wednesday, 15 APril 2026 | 10:00-10:30 AM | Online
Your traditional security isn’t stopping today’s attacks. Here’s what will.
The Problem Every NZ Business Faces
Your business has antivirus software. You have firewalls. You’ve implemented email filtering. Yet cybercriminals are increasingly successful at bypassing these traditional defences using sophisticated techniques that don’t trigger conventional security alerts.
The uncomfortable truth? Most modern breaches happen despite having security measures in place. Attackers aren’t breaking down your doors—they’re stealing legitimate credentials and walking right through them.
Understanding Managed Detection and Response (MDR)
- Why assuming threats will get past your defences is smarter than assuming they won’t
- How continuous monitoring and expert threat hunting catch what traditional security misses
- The difference between having security tools and having someone watching them 24/7
- Real-world example: How rapid detection prevents ransomware from spreading
Understanding Identity Threat Detection and Response (ITDR)
- Why 80% of breaches now involve compromised credentials, not technical exploits
- How attackers use legitimate accounts to move through your systems undetected
- What makes identity systems uniquely vulnerable and why they need specialized protection
- The attack patterns ITDR stops: credential theft, privilege escalation, lateral movement
How These Work Together
- Why you need both environment monitoring (MDR) and identity protection (ITDR)
- How layered security creates comprehensive defence against modern attack methods
- Practical guidance on when your business needs these capabilities
- What to look for in MDR/ITDR solutions and providers
Who Should Attend
This webinar is designed for:
- Business Owners & Executives who need to understand modern cybersecurity without technical overwhelm
- IT Managers evaluating whether current security measures match today’s threat landscape
- Finance & Operations Leaders responsible for risk management and business continuity
- Anyone who’s wondered whether their cybersecurity is actually adequate for 2025
No technical background required. We’ll explain everything in business terms that make sense.
What You’ll Gain
By the end of this webinar, you’ll have:
✓ Clear understanding of what MDR and ITDR actually do (and why acronyms matter less than outcomes)
✓ Practical framework for evaluating whether your current security provides adequate detection and response
✓ Real-world context for how these capabilities stop attacks traditional security misses
✓ Confidence to have informed conversations about your organization’s security posture
✓ Actionable next steps for strengthening your defences without unnecessary complexity
On-Demand Webinar Replays
Catch up on our most popular training sessions, available anytime:
Your (Home/Small Business) Router Could Be Working for Criminals Right Now
Right now, somewhere in the world, a home or office router is quietly routing cybercriminal traffic, and its owner is completely unaware. That's the reality revealed by the discovery of KadNap, a sophisticated malware campaign that has become one of the most...
When Geopolitical Conflict Becomes Your IT Problem
Lessons from the Stryker Cyberattack A global medical technology company. 56,000 employees. Operations in 60 countries. And in March 2026, systems wiped across every one of them — not because of a data breach or ransomware, but because of a school bombing in Iran....
When AI Becomes the Attack Tool
What the Mexico Government Breach Means for Your Business A cyberattack that unfolded over December 2025 and January 2026 has changed how security professionals think about AI . New Zealand business leaders should take note. A single attacker jailbroke Anthropic's...
A Revolution in Copilot: Adding “Tasks” goes from AI Answers to AI Action
From AI Answers to AI Action For the past year, Microsoft Copilot has helped people draft emails, summarise meetings, and analyse documents. Now Microsoft is taking the next big step with Copilot Tasks. This is a new capability that moves Copilot beyond...
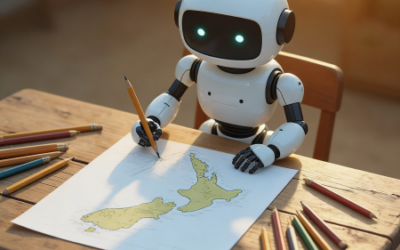
How Small Businesses in New Zealand Are Using AI — And What’s Holding Them Back
Artificial intelligence has moved from buzzword to business reality for New Zealand organisations, but the picture is more complicated than the headline numbers suggest. While adoption figures look impressive on paper, a sharper divide is emerging between businesses...
Your Phone Is a Target
Why Mobile Security Can't Be an Afterthought Think about everything on your smartphone or tablet right now: your email, your banking app, Microsoft 365, client communications, multifactor authentication codes, and a direct line into your company's cloud systems. Now...
10 Windows Shortcuts That Will Save Your Team Hours
Most people learn a handful of keyboard shortcuts early in their careers and stick with them forever. Ctrl+C, Ctrl+V, maybe Alt+Tab if they're feeling adventurous. But Windows has quietly accumulated a powerful set of shortcuts that most business users have never...
5 Microsoft 365 Features That Solve Real Business Problems (No AI Required)
Since October 2025, Microsoft has rolled out more than 1,100 features across Microsoft 365, Security, Copilot, and SharePoint. It's hard to keep up! While much of the attention focuses on AI capabilities, some of the most practical improvements are the foundational...
Webinar Replay: Decoding SMB1001. Understanding Your Cybersecurity Maturity
Cybersecurity certification doesn't have to be complex or overwhelming. Understanding SMB1001: What is SMB1001 and why it was created specifically for organisations like yours The five certification levels (Bronze to Diamond) and what each means for your organisation...