Free IT Training Events: Expert Webinars & Workshops
To keep you informed.
Upcoming Live IT Training Events
AI Innovation Circle (Free)
Join other business managers in an honest, collaborative exploration of AI. No sales pitches. No unrealistic promises. Just real businesses sharing their genuine experiences, challenges, and solutions.
NExt Session – Thursday, 26 March 2026
Story circle format where participants share their AI journey so far, address myths and fears, and form exploration partnerships. Focus on honest discussion about what AI actually means for small businesses.
(Free) Webinar – Beyond Antivirus: Understanding MDR and ITDR for Modern Cyber Defence
Wednesday, 15 APril 2026 | 10:00-10:30 AM | Online
Your traditional security isn’t stopping today’s attacks. Here’s what will.
The Problem Every NZ Business Faces
Your business has antivirus software. You have firewalls. You’ve implemented email filtering. Yet cybercriminals are increasingly successful at bypassing these traditional defences using sophisticated techniques that don’t trigger conventional security alerts.
The uncomfortable truth? Most modern breaches happen despite having security measures in place. Attackers aren’t breaking down your doors—they’re stealing legitimate credentials and walking right through them.
Understanding Managed Detection and Response (MDR)
- Why assuming threats will get past your defences is smarter than assuming they won’t
- How continuous monitoring and expert threat hunting catch what traditional security misses
- The difference between having security tools and having someone watching them 24/7
- Real-world example: How rapid detection prevents ransomware from spreading
Understanding Identity Threat Detection and Response (ITDR)
- Why 80% of breaches now involve compromised credentials, not technical exploits
- How attackers use legitimate accounts to move through your systems undetected
- What makes identity systems uniquely vulnerable and why they need specialized protection
- The attack patterns ITDR stops: credential theft, privilege escalation, lateral movement
How These Work Together
- Why you need both environment monitoring (MDR) and identity protection (ITDR)
- How layered security creates comprehensive defence against modern attack methods
- Practical guidance on when your business needs these capabilities
- What to look for in MDR/ITDR solutions and providers
Who Should Attend
This webinar is designed for:
- Business Owners & Executives who need to understand modern cybersecurity without technical overwhelm
- IT Managers evaluating whether current security measures match today’s threat landscape
- Finance & Operations Leaders responsible for risk management and business continuity
- Anyone who’s wondered whether their cybersecurity is actually adequate for 2025
No technical background required. We’ll explain everything in business terms that make sense.
What You’ll Gain
By the end of this webinar, you’ll have:
✓ Clear understanding of what MDR and ITDR actually do (and why acronyms matter less than outcomes)
✓ Practical framework for evaluating whether your current security provides adequate detection and response
✓ Real-world context for how these capabilities stop attacks traditional security misses
✓ Confidence to have informed conversations about your organization’s security posture
✓ Actionable next steps for strengthening your defences without unnecessary complexity
On-Demand Webinar Replays
Catch up on our most popular training sessions, available anytime:
Which of these new features in Windows 11 will save you time?
Which of these new features in Windows 11 will save you time?
Microsoft are gradually rolling out new Windows 11 features to Beta users, This means that the rest of us can expect them sometime later in the year.
Don’t let these common security gaps take your business down.
We’re only a few months into 2025, and already we’ve seen businesses hit hard by cyberattacks they could have prevented. Every time we conduct IT security checkups, we find the same critical vulnerabilities—gaps that could lead to serious downtime, data loss, or...
Has Outlook “classic” been dropped from Microsoft 365?
Late last year, we commented on the new Outlook, and how it wasn’t being appreciated as much as Microsoft might like.Our view on this has only been reinforced with most clients preferring the ‘classic’ version that we are all used to.We’re now seeing that the Classic...
AI Digest: February 2025
The AI race steams on in February. Our Kambium Consulting colleagues are tracking the world of AI and keeping us abreast. Here's the summary for Feb 2025 in case you missed it. Firstly the adoption in sales is compelling. That makes sense. Sales people have to...
NCSC warns law firms
It’s not surprising that legal practices are targeted by cyber-criminals.By their very nature, they hold considerable amounts of private “PII” data (personally identifiable information). On top of that, law firms are typically busy, pressured environments where it is...
Webinar Replay – What are the NZ Government recommendations for SME Business cyber-security?
What are the NZ Government recommendations for SME Business cyber-security? How does your business match up?CertNZ has been rolled into the new National Cyber Security Centre. They've released the 10 Critical Controls and a Cyber-Security Framework? What do they mean...
That day when a Kinetics client DIDN’T get hacked.
We’ve just wrapped up a security investigation for one of our amazing clients. All of our clients are amazing, but as you read this story, you’ll see why we’re especially proud of this client. We’ve anonymised it out of respect, although this story reflects really...
Internet Alert – Chorus Maintenance – Planned Events 10-18 February 2025
Chorus have planned maintenance occurring across their network. This MAY impact your internet connectivity. We have scheduled to check all systems on the morning after these windows and will proactively respond to any alerts we receive. Date Time Estimated...
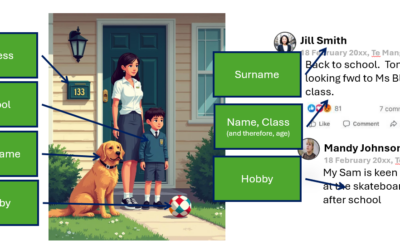
The Hidden Dangers of Oversharing Family Photos on Social Media
In today's online age, sharing family photos on social media has become a common way to stay connected with loved ones and document precious moments. But beware of ‘Oversharing’ There is a huge danger that this seemingly harmless activity can expose you and your...