What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
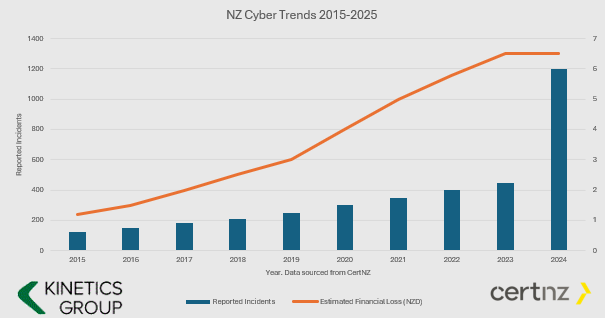
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”

What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning

Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up

How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
New Zealand’s AI Revolution: How Artificial Intelligence is Transforming Productivity in 2025
New Zealand is experiencing a remarkable transformation in 2025, with artificial intelligence driving unprecedented productivity gains across diverse industries. According to recent surveys, 82% of New Zealand organisations now use AI in some capacity, representing a...
AI-Driven Productivity Gains in New Zealand (2025)
New Zealand’s businesses are experiencing notable productivity increases in 2025 due to the use of Artificial Intelligence (AI). Across diverse industries – from manufacturing floors to rural farms – AI technologies are streamlining operations, cutting costs, and...
Webinar Replay: A real world guide to AI
You’ve heard the hype on how amazing AI is, and then you tried it and were… underwhelmed. Or maybe you’ve read how dangerous AI is, and so you don’t want anyone in your organisation to risk using it. So, what is the AI reality for people that work in small to medium...
EchoLeak: What It Is, Why It Matters, and Why You Can Still Trust AI
The excitement around AI is plain to see, but it is tempered by an understandable caution. Many readers will be using AI to work smarter—from writing emails to analysing reports. But the caution is appropriate. Just like any powerful tool, AI needs to be used...
Have you considered the extent to which your business already depends on AI?
AI may be subtly operating behind the scenes, without your awareness. From tools that draft emails or streamline customer support to applications that analyse data trends or enhance productivity, AI is increasingly becoming an integral component of modern professional...
Drowning in Emails? 6 Tips to Conquer Your Outlook Inbox & Reclaim Your Time
Let's face it: for many of us, the Outlook inbox has become a digital black hole. Notifications ping, numbers climb, and the constant pressure to respond can feel overwhelming. It’s a modern workplace reality, but it doesn't have to control your day. You can regain...
June 2025 Report: Cyber is now the THIRD largest economy in the world
As we approach the midpoint of 2025, New Zealand’s cyber security landscape continues to evolve rapidly. With digital transformation accelerating across sectors, the country faces a growing array of cyber threats—ranging from financially motivated scams to...
AI Innovations and Legal Battles: A Month in Review
AI Innovations and Legal Battles: A Month in Review This month has been a whirlwind of advancements and legal drama in the AI industry. Alibaba's New AI Models Alibaba kicked off the month by unveiling Qwen3, a new family of AI models that reportedly match, and...
A practical guide: How much cyber security investment do I really need?
Cyber costs seem to keep increasing every year. There is always something more that is needed. Organisations can’t afford to over-invest but they can’t afford to under-invest either. It’s a tightrope so we thought it would be useful to prepare a simple guide.A...
To use, or not to use, AI to transcribe a meeting.
We understand that capturing the details of meetings is crucial. But manual note-taking is time-consuming, prone to errors, and often leaves important nuances lost. Enter AI transcription AI Transcription is a rapidly evolving technology promising accurate, efficient...