What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
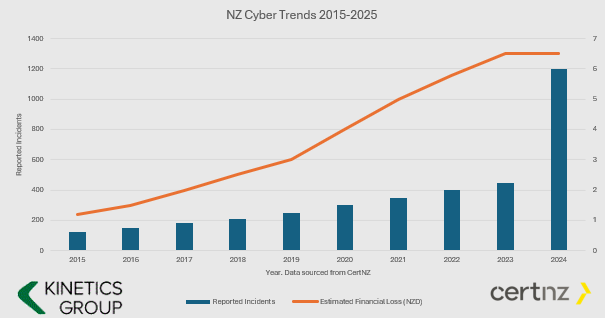
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”
2
What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning
3
Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up
4
How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Giving clients better response times
[header2 text="Speeding up our service" align="left" color="#336A40" margintop=""] To speed up our service, we’ve introduced a new ‘ticket’ (job) logging system. This is in additional option to ringing us or emailing our ‘support’ email team. Each of these systems...
New cool stuff in your Office 365
[header2 text="New stuff, all the time" align="left" color="#336A40" margintop=""] Microsoft are continually updating Office 365 with awesome new tools and more efficient ways of working. Keeping up with these and learning how to use them is a big challenge, which is...
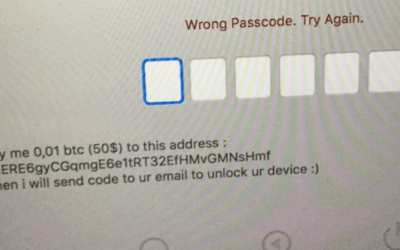
Macs are the latest victims of ransomware
According to Veeam the number of ransomware attacks has jumped 6000% since 2015-16. There is an interesting correlation between the increase in ransom attacks and the increase in value of bitcoins! Bitcoin value in NZ dollars. Source Google Finance Now we...
Seamless migration to cloud file storage
"We've been very fortunate to have them on board. Our transition went very smoothly. There was a great sense of comfort about them and they are very professional in what they do." - Jeremy Sole, CEO SharePoint migration Making the change from local file storage to...
Member training for the EMA
"For anyone thinking of using Kinetics for training : you're going to get value for money, on topic training. Definitely thumbs up." - David Foley, EMA Learning Manager Member IT training The EMA turned to Kinetics when they wanted to provide members...
No excuses for ugly PowerPoint slides
Add a design eye to give some pizzazz to your PowerPoint Not everyone has an eye for design – particularly when it comes to PowerPoint. Now you can get PowerPoint to design your slides for you. 1. Add the text and content you wish to display on your slide. The...
Sensing your office Vibe
As Kinetics had grown, our ability to understand what everyone in the team is feeling or thinking has diminished. The distance that growth brings between staff and managers creates doubts and misunderstandings that can be hard to see. More and more we have...
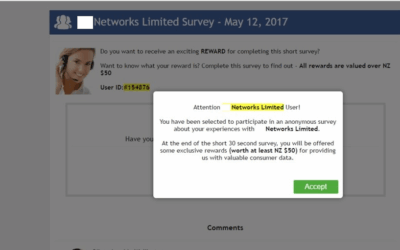
BEWARE THE FAKE LOGIN
Most people will be familiar with the concept of linking something to your Facebook login. Many sites offer you the opportunity to login using your Facebook account. Scammers use this concept to farm credentials for other sites. One we have started seeing more...
Microsoft 2017 Country Partner of the year!
[header2 text="THE SECRET TO OUR SUCCESS... IS OUR CLIENTS" align="left" color="#336A40" margintop=""] On top of our recent Cloud Productivity award, Microsoft have just announced Kinetics as their overall New Zealand 2017 Partner of the Year. We love doing what we...
A simple but effective hack is back
[header2 text="We've seen this several times in the last few weeks" align="left" color="#336A40" margintop=""] A classic phishing technique has been updated and is reaping rewards for hackers. Delivery is by email or web popup. You are asked to take a survey (often...