What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
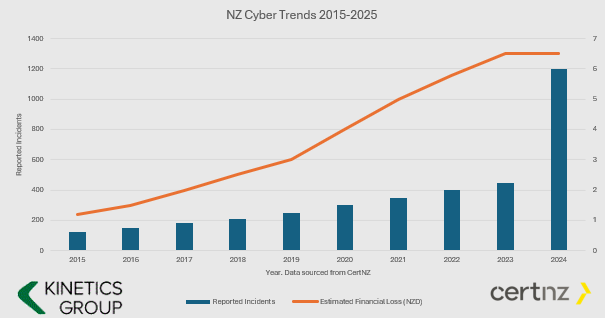
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”
2
What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning
3
Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up
4
How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
WE ARE GROWING
1 September 2018 Kinetics Group Limited and Wired Dog Limited announced today that they have joined together as one IT managed services and advisory provider. Operating under the Kinetics Group brand from 3 September 2018, the combined team will operate from...
Cloud – Kiwi-made or a global players like AWS or Azure?
Cloud cloud cloud, our customers must get sick of hearing us bang on about it! But we keep talking about it because the cloud gives fantastic options to most businesses to do more than ever, for less cost. But, not all clouds are the same. Regular readers will...
Not as exciting as last month, but still pretty cool! Translate and Activity.
Last month we highlighted the new 'dictation' feature in Office - Outlook and Word, and it seems heaps of our readers and clients have embraced it! This month, we've looked through all that's new with Office 365 and we're going to highlight some useful features -...
We’re going to be hearing about data privacy for a lot longer yet!
I don't know about you, but every day I open emails and articles about data security and our obligations in business. It's feeling a little overwhelming, but on closer inspection, most of the conversation is pretty sensible. The headlines have been the data breach...
Overloading in Outlook? Focussed Inbox is the answer!
Is your inbox overflowing? Once things move down the page, do they disappear, accompanied by the nagging guilt that you should have done something? You need a focussed inbox. For many people, their inbox becomes part of their filing cabinet, and that's obviously not...
Letter from Microsoft Inspire – Vegas 2018
It wasn’t just the weather that was hot. Microsoft is hot right now, and given how much we all rely on them for the tools to run our businesses, that's an exciting prospect. While there weren't specific announcements, what I found encouraging was the consistent...
The best new thing in Office that no one knows about (Shush – don’t tell)
Spoiler alert- you have to read the full article - and good news alert – the article is really short! Office 365 keeps changing. Updates and upgrades happen when you aren’t looking. While many of them are pretty trivial and only impact a few people, some updates are...
When does Windows 10 become Windows 11?
When Microsoft released Windows 10, they said it would be the last version – but that hasn’t stopped them enhancing it. The updates available in the April 2018 (Version “1803”) release continue to refine it in small but useful ways that add up to a significant...
What’s in an Antivirus? ( or, when is ‘free’ the most expensive option?)
It is not uncommon for us to be asked why a business needs to purchase antivirus when Windows 10 already includes antivirus. It's true - Windows comes with a 'free' antivirus - Windows Defender is free with Windows and has been for some time. [header2 text="It...
Sneaky devils – how insecure email led to a $150K loss
Recently I was lucky enough to spend some time with a group of my Ozzie peers. One of the things we did was share problems and solutions. During those discussions, I heard of the following hack. [header2 text="This is not a made-up story. It is true and I know of...