What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
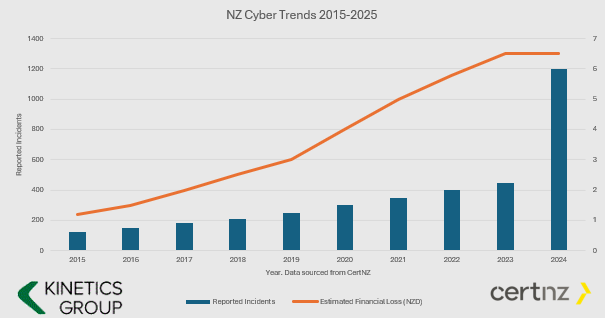
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”

What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning

Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up

How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
October 2025: Five AI Breakthroughs to change how businesses work
October 2025 was another big month for AI. We’ve picked 5 that stand out to us for highlighting. These five advances deserve your attention because they're already being integrated into tools your team likely uses daily. Here's what changed in October, and why it...
Beyond Anti-Virus: Understanding EDR and MDR for Your Business
"Do we have anti-virus?" It's one of the first cybersecurity questions business leaders ask. For many years, it was the right question. But in 2025, if anti-virus is your primary cybersecurity defence, you're bringing a lock and key to a sophisticated break-in. The...
Webinar Replay: From Firefighting to Future-Ready: Transform Your IT from Reactive Support to Strategic Business Driver
Does it seem that your IT team constantly putting out fires instead of preventing them? Are technology decisions being made in isolation without clear connection to your business goals? You're not alone. Watch this webinar recording where we'll reveal the critical...
SpamGPT: When AI Becomes a Phishing Playbook—And How to Protect Your Business
For years, we've told businesses to watch for telltale phishing signs: poor grammar, suspicious sender addresses, generic greetings. But what happens when cybercriminals have access to the same sophisticated AI tools your marketing team uses—except weaponised...
Training AI to Write Like You: A Strategic Guide to Developing Your Digital Voice
Your writing voice is one of your most valuable professional assets. It builds trust, conveys expertise, and creates connections with clients, colleagues, and stakeholders. But here's the challenge: as AI writing tools become essential business productivity tools, how...
AI’s Big September Moves
If you’ve been following the AI space lately, you’ll know it’s moving at a cracking pace. Just this month, xAI dropped Grok 4 Fast—a model that’s all about strong reasoning, but at a fraction of the cost. We’re talking 98% cheaper than its predecessor, Grok 4, for the...
Sign up now for New Zealand Cyber Smart Week
New Zealand Cyber Smart Week 2025: Oct 6-12 Transform Your Business Security The countdown is on. In just a few days, Cyber Smart Week 2025 kicks off (6-12 October), and New Zealand businesses have a crucial opportunity to strengthen their cybersecurity posture. But...
Will Microsoft’s Secure Score Requirements for IT Partners impact you?
Microsoft Secure Score Requirements for MSPs: What You Need to Know by October 2025 Microsoft is raising the security bar for Managed Service Providers (MSPs) like Kinetics Group,and the deadline is approaching faster than many realise. Starting October 1, 2025, MSPs...
Webinar Replay: Transform, Grow & Thrive — How Kinetics is Using AI to Boost Business Productivity
Rewatch our short webinar showcasing how Kinetics is harnessing the power of AI to elevate productivity, streamline operations, and safeguard sensitive data.Key Links: Next Events Webinar Slideshow Free AI Copilot Guide In this session, you'll discover: Real-world...
Is Your IT Strategic Enough? The Reality Check Most NZ Businesses Need
Your systems work. Problems get fixed. Your IT person seems busy. So why does technology still feel like a cost centre rather than a competitive advantage? If this sounds familiar, you're not alone. Most New Zealand businesses are stuck in what we call the "Technical...