What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
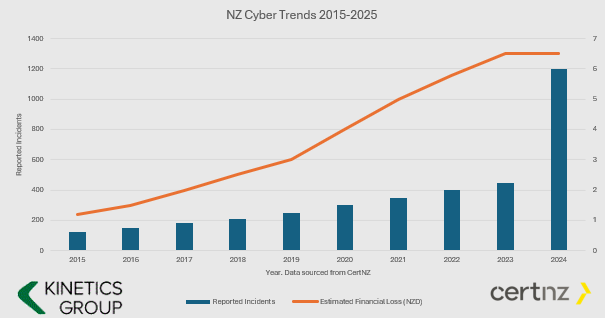
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”
2
What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning
3
Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up
4
How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Why old versions of Microsoft Windows and Microsoft SQL are putting you at risk
Modernise your infrastructure and future-proof your technology Prepare for Windows Server 2008 and SQL Server 2008 end of support With the end of support for Windows Server 2008 fast approaching, and SQL Server 2008 recently expired, now is the time to start...
Why you should care about BlueKeep
Regular readers will know that we are fanatical about updates and patches for all critical software. The world is more connected and the cyber-crime community is more organised and determined than ever. If you think cyber-criminals are teenage kids working from home,...
9 Common Excel Mistakes
We were reminded of the risks of messing up spreadsheets in a recent blog post at Oracle: The scary fact they quote is that 88% of all spreadsheets are wrong! The consequences of relying on bad information as a result can be insane! That reminded me of a couple of...
Feeling less Vulnerable
When the Microsoft cloud had a momentary failure in early May, most of us had an uncomfortable hour with limited access to our files and systems. It seems that some red-faced engineer at Microsoft made a simple small mistake that impacted systems all around the...
RIP Windows 7, SQL 2008 and friends
It's time to say goodbye to Windows 7 The end of the (support) road is approaching rapidly. They are over ten years old which is ancient in IT terms. If you think about tech around your home or in your daily life, then its quite understandable that these products...
The alarming business models of cyber-criminals
Cyber-crime has become big business It's organised, and the purveyors are shameless in their determination to steal from all of us. Heaven only knows where they get their names from. One group we recently became aware of is called 'PINCHY SPIDER', and they are doing...
Anyone can be hacked! And anyone can be the cause.
Guess who got hacked? In recent articles, we’ve warned that people are the weakest link in your IT security. We’ve also warned that any business is a target. No one is immune. Tech companies like us are especially cautious because, in order to do our job, we have...
Updated Privacy Laws coming to NZ
Overshadowed by overseas privacy law changes like GDPR, our own NZ Privacy legislation has flown a little under the radar. But rest assured, changes are coming here as well. The last change in NZ Law was 1993, and it was world-leading at the time. Then in 2011, the...
Te Whangai – Growing People by Growing Plants
We are incredibly proud to have helped The Te Whangai Trust. They are an amazing organisation. There’s a whole group of society that miss out on the opportunities many of us take for-granted. While many under-privileged members of our community can access various...
Using the Cloud to compete globally from New Zealand
As a small kiwi business working in a global context, The Conference Company (TCC) faced some unique challenges. They compete around the world to host some of the most pre-eminent events against impressive competition from much larger operations. TCC has to present...