What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
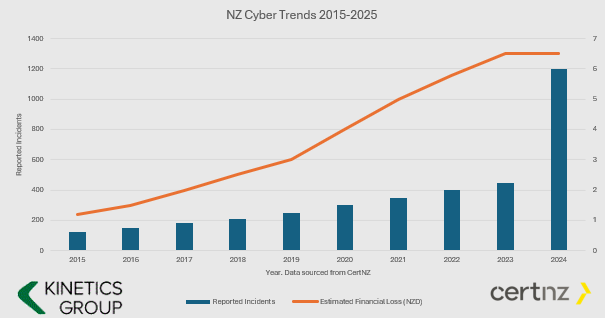
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”
2
What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning
3
Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up
4
How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Windows 10 1909 – what’s in the latest update?
At last – Windows 10 1909 – the long awaited second Windows 10 update for 2019. Were you waiting for it? Actually it’s unlikely! In fact the first update, from March, is only just rolling out now, so it will be some time before this version hits your PC or laptop....
“Request for Information” warning
A recently released report on the Botnet 'MasterMana' has highlighted a simple but effective social engineering technique. MasterMana has been spreading via emails requesting information on products or services offered by the target company. The email is...
Eliot Sinclair Case study – FlightPlan (Best Practice Review)
Overview Eliot Sinclair & Partners (ESP) provide surveying, engineering, planning, landscape architecture and urban design consulting. Headquartered in Christchurch, New Zealand, Eliot Sinclair have provided consultancy services across South Pacific and Asia with...
Those scamming so and so’s
In September, Kinetics held a lunchtime IT security event focused around a presentation by our CTO Bill Lunam. After taking us though an abridged history of the internet, and an update on the current status of Internet crime, Bill explained some specific’s around the...
Microsoft Update – Backup Authenticator (Two-factor authentication tool) and Window 10 1909 ?
Firstly, unless you just delete our emails, or ignore what we (and every other tech professional) have been saying, you should now be using 2FA (two factor authentication) on pretty much everything, especially your Office365. The downside is that you don’t want to...
Bigger than Texas?
Its easy to think of security as something that’s only for larger organisations. They can afford the fancy systems that lock down networks, wireless connections and endpoint PCs & mobile devices. After all, aren't they the only organisations that hackers target?...
Compare two (near) identical Word files, without going insane
Of course, in a modern cloud world, this shouldn’t happen! We should share a link to a file and use versions to maintain it’s history. But we’re not in a perfect work, and we often get multiple people updating copies of the same file. Its all good until we have to...
Scamming your payroll
Keep an eye on your payroll! We're hearing about a bold new scam in the US, but it's bound to come to our shores soon. It's probably more likely to be effective in larger businesses or ones with an outsourced payroll. Essentially, the scammers try to intercept staff...
Would you click on either of these?
You are most vulnerable when you are busy, frantically jumping from call to call, meeting to meeting, distraction to distraction. So when you get a dodgy email, it's very easy to open it. This morning, that was me! And, even as hyper-aware as I am, I still...
Is your phone one of the 25M infected Android phones?
Watch your phone! Agent Smith is the name of the somewhat dry villain character in the Matrix movie trilogy from the late 90's. He appears everywhere, instantly, taking over legitimate personas and replacing them with himself. So is a well-named virus (actually...