What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
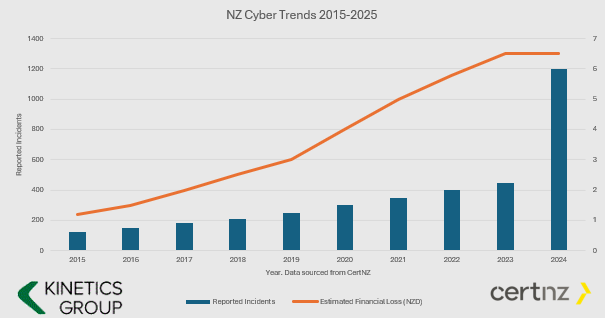
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”
2
What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning
3
Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up
4
How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Where’s my new laptop?
While stocks last! What is happening to supplies right now? We're experiencing an unprecedented shortage in new IT equipment. At this rate, they seem a prime candidate for 2021's 'toilet paper.' Never has "while stocks last" been so apt! Global supply chains are...
Another drawing pen app from Microsoft and why you should use OneNote and Whiteboard
Collaborate more efficiently Microsoft Garage is their ‘skunk works’ programme to encourage employees to do things they care about. Small teams run their own ideas and trial them – a bit of an ongoing Hackathon. Many of these ideas go on to become part of Microsoft...
Bursting the bubble – what to think about before crossing the ditch?
With the Australian travel bubble opening up, many people are starting to think about heading across to see family, friends or business partners. The government has been very clear about their traffic lights, and a “flyer beware” stance, so we’ve got to be a little cautious and plan ahead. You might be planning to head across for just a day or two, but its prudent to be prepared for a longer stay.
FVLB – Migration to Azure Cloud Services
Overview The Film and Video Labelling Body (FVLB) is a not for profit organisation that is responsible for rating films that are made available to the public. The Labelling Body: Rates unrestricted films Cross-rates unrestricted films that have been rated in...
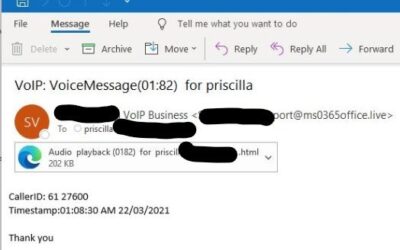
Don’t click!
We're seeing this phishing attack over and over this week. Your first clue that something is wrong is it doesn't look like voicemail emails you might typically receive. Unless you have a brand new voicemail/phone system these shouldn't change format! The second clue...
Zero-Trust IT Security
'Zero-Trust' is a tough headline. Zero-trust in a world where we trust people all the time is an unpleasant concept. We trust that when we order a package online, that the vendor will take our order and not just our money, that our product will be passed to a courier...
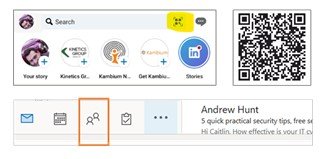
We are who we know
Managing contacts has become more important than ever. Here’s a few tips on how to make use of smart tools built into Outlook: 1. Rather than exchange business cards (so last century)... Share your contact details using Linked In – just hit the box on the right of the...
What is “Dark Mode”? Why should you consider it?
With all our warnings about cyber-hackers, you’d be forgiven for thinking this was another hazard. But no! Dark Mode is a good thing! You can activate it on Windows 10 by going to Settings – Personalization – Colors and picking Dark. Most phones also offer the same...
What does IT mean to you?
Who do you call when you need to : update your IT usage or data privacy policies manage your internal IT staff? select new business software, e.g. CRM or financial software? accelerate a process or break a business processing log-jam? Traditionally businesses think of...
5 simple steps to stay cloud-cyber-secure
We’ve posted repeatedly about cyber-security and the need to be more vigilant and more careful, and we’ve shared real-world stories to reinforce the concern. It’s a concern then that we still see a number of organisations that remain reluctant to increase their...