What expert cyber-security does my business need?
1
The inconvenient facts about Cyber Security
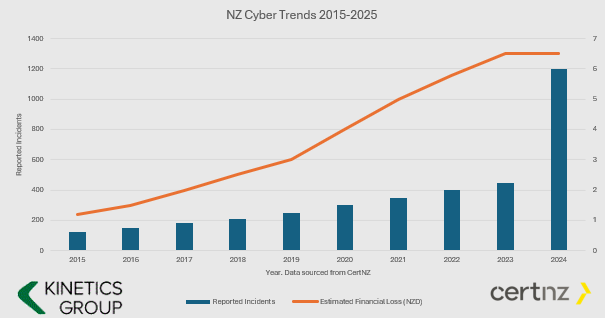
- The number and value of incidents is increasing.
- Cyber Crime is BIG business and they keep investing in new tools.
- If you aren’t keeping your defences up, then it is only a matter of time before you fall victim (i.e. if your cyber protection is the same now as it was even just one year ago, then you are increasingly vulnerable.
- You have to ward them off every hour of every day, they only have to get through once.
You might say this is scare-mongering. If all this hacking is going on and nothing has happened yet, then surely I don’t need to worry?
We’d say “good luck to you – why do you have seat belts in your car? – its only a question of time.”
2
What Cybersecurity Protection Level Do You Need?
Q: Does this mean I don’t need cyber-insurance? A: You still need cyber-insurance. We can only reduce your risk (and most insurers will want to see these protections in place before they will offer cover)
Q: What is involved installing KARE? A: Once a PC, Mac, Tablet or Phone is ready, our scripts run every time you login and the security tools auto-install – with configuration for corporate devices and BYOD.
AD HOC
STRUCTURED LAYERS based on the CertNZ Critical Controls Framework
For organisations in the cloud with minimal reliance on IT.
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect.
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough.
Add in depth reporting, server backup and identity monitoring.
Pick KARE FOUNDATION SME
For organisations that value a structured, proactive and comprehensively protected IT.
Add more scrutiny and awareness, personalised cyber training and business planning.
For organisations in the cloud with minimal reliance on IT
Everything is in the cloud. There are only a few PCs/Macs and iPhones/Androids to protect
For organisations in the cloud, and maybe a small number of servers, looking to be more thorough
Add in depth reporting, server backup and identity monitoring
Pick KARE FOUNDATION SME
For organisations who value a structured, proactive IT engagement
Add more scrutiny and awareness, personalised cyber training and business planning
3
Enhanced Security Services & Add-Ons
+ Choose additional services as required
Add Fixed Monthly Support Fee
No cost surprises. One fee for all business-hours support
(excludes projects and training)
Add Managed Firewall
Network firewall
Kinetics supplies and manages on a monthly contract
Add Password Vault
Organisation Wide
Maintain unique, complex passwords for all users and/or shared with teams
Add 365 Cloud Backup
Content backup for 365
Go over and beyond the standard Microsoft backup protection
Backup and Continuity
A range from backup to stand-by services
If you have servers, you need to back them up
4
How about the broader cyber-framework?
Comprehensive Data Protection & Compliance
Platform Security is just part of a broader cyber-security and data protection framework.
Have you considered how manage your data within your Microsoft tenancy? How’s your Microsoft “Secure Score“? As you get the external security set up, let us work with you to manage the other side – your internal security.
Our consultants can work with you to understand what data your organisation maintains, and the obligations (and client expectations) and the rules that need to be established to protect it. Who should have access to which libraries? What can be shared and what can’t be. How do you work with external partners and protect your content?
We can document your data policy, prepare your data privacy policies, incident response plans and data management structures, and we can set up compliance regular reporting.
We’ll implement the policies in your 365 and manage your data to make sure it’s where it should be, not suffering from duplication confusion or unintended leakage
Data Management
The tidier your data, the easier it is for AI to use it well to accelerate your productivity
Download our latest executive “10 minute” briefing to share with colleagues

Latest Cybersecurity Insights & Resources
Does your firm have the right relationship with your IT provider?
Regardless of whether your IT provider is your in-house IT team or a trusted business provider, do you have the right relationship with them? The right IT provider will ask "WHY" long before they ask "WHAT" and will be focused on proactively adding value to your...
Does your firm have an appropriate Data Privacy Policy?
Data Privacy is now a hot topic in NZ. As a law firm, you will be more aware of the legislation than us, but we have been astonished that not every firm seems to understand the ramifications for their own work product. You will know what is driving our concern:...
Who really controls your firm’s IT systems and your data?
You know who owns and leases your operational equipment, or your buildings, plant and other physical facilities. Can you say who controls your IT? How flexible is your IT supply chain to meet your partnership's ongoing needs? Given how vital IT is to your legal...
IT is more than silicon – have you ever stress tested the human side of your firm’s I.T?
Every chain relies on every link, and the stronger each link, then the stronger the chain - hence the saying about the weakest link. Your IT chain has people - we need to think about them - the IT staff, the users, and of course the management structure around them....
Are you maximising your firm’s technology investment?
When your firm last made a significant IT investment, you had a clear understanding of why you made it and the return you were seeking to achieve. You might even have had to justify it to a partners' committee and make various assurances that it was the best thing...
Are the appropriate IT Governance controls in place to protect your Firm’s Value?
In most organisations, and law firms are no exception,, IT has grown organically, meeting business needs as they arise. Those demands have come through thick and fast from almost all areas of the organisation's operations. IT has become integral to almost all...
Obligations to the firm’s Partners and Management
Are you meeting your obligations to your firm's stakeholders? Until relatively recently a law firm's management committee typically only got involved with IT when the management wanted to proceed with a major capital investment - a system refresh, new practice...
2021 Trend Reports confirms cyber-security advice
How many people DON’T report ransomware attacks? It’s too early to see the Q42021 results from CertNZ but their Q3 report tells there were 2,072 incidents that they responded to in Q3 and fraud/scam’s were up 25%. Their report confirms that the very risks we have been...
Hackers Caught! Millions Seized
Crime doesn’t always pay. The FSB reports (if you can read Russian) that they have taken down the “Revil” band of hackers. These are the people that have caused absolute havoc, from disrupting the US oil pipelines, to the Kaseya attack that took out businesses all...
Kinetics COVID Policy
Our Covid-19 approach. A number of clients and partners are asking us about our Covid-19 policy, so we thought we'd share it! Like many workplaces, we've extensively consulted our team and worked through their range of views. Our workplace requires all visitors...