Your own personalised stalker
It always seemed slightly creepy that your computer shows advertising that is strangely accurately targeted at things you might have been interested in. On the surface, that seems quite useful. If you have to tolerate ads on your screen, at least having them show things you were interested in seems helpful.
Instead, we wonder how the system knows. It feels like a breach of our privacy.
It all starts when you install an app, and it pops up a question asking for permission to use your location, and/or your camera and/or your microphone.
This is useful for advertisers. For example, they can use your location. If the app reports this back to the content provider, they can match up your location and compare you to other people nearby. If you tend to go to the same places as other people, you are probably interested in the same things, so an advertiser might use that assumption to present advertising to you, or other people that you spend time with.
That does sound a bit overreaching, but we reluctantly agree to the presented terms simply because we want to use the app. If that is a condition of use, and we want to use the app, then we agree.
So, now we are seeing consumers getting the choice to push back.
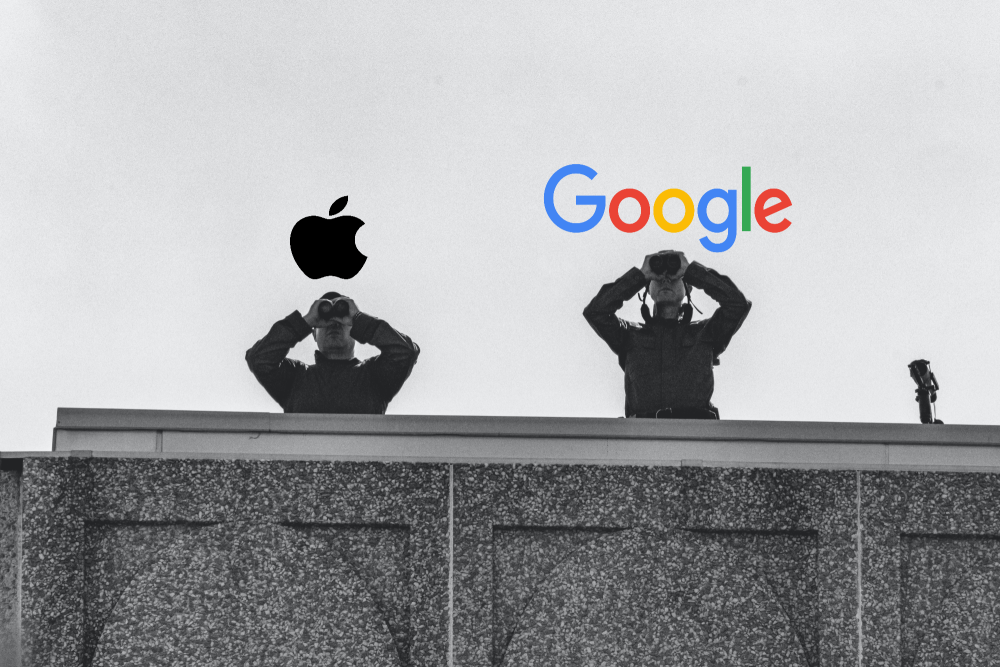
Apple
Now, with iOS15, Apple are saying that you will get to see what apps are accessing your data. You will be able to see when an app used that permission, and there it was sent to. Whether that list of third party sites is any use or not is meaningful is unclear.
Not quite as advanced but following quickly behind is Google Android. With Android 12, you will have the option to de-personalise your data. They will still track usage, but won’t link it back to you.
Is there any truth to the rumour that your phone or TV is listening to you, and presented content based on private conversations it overhears?
Given how poor the voice recognition is on phones , cars, or tools like Alexa or Siri, its pretty evident this can’t be reality. If it, is, then heaven only knows what it thinks it’s hearing. The voice recognition tools are getting better all the time, but there is a long way to go.
IT is more than silicon – have you ever stress tested the human side of your I.T?
Every chain relies on every link, and the stronger each link, then the stronger the chain - hence the saying about the weakest link. Your IT chain has people - we need to think about them - the volunteers, the staff users, and of course the management structure around...
Are the appropriate IT Governance controls in place to protect your community value?
In most organisations, IT has grown organically, meeting business needs as they arise. Those demands have come through thick and fast from almost all areas of the organisation's operations. IT has become integral to almost all aspects of operations in most workplaces,...
10 IT Questions for Not-For-Profit Organisations
How does IT make your NFP more successful? Not -for-profits come in all shapes and sizes in New Zealand and many of us are involved in many of them - supporting our community in ways that resonate for us. Not for profits measure success differently to other...
Latest trend – hacking Teams
Over a quarter of a billion people use Teams every month. Under the current lockdown/isolate/work-from-home regimes, it is a vital tool for most of us. Many organisations including us even use it for our phones because it is so flexible and excellent value. You can...
Are you managing ALL your critical IT?
IT is critical to the operation of almost every organisation. If your IT is more than computers and mobiles then this webinar is for you. If IT is a critical asset to your organisation, then this webinar is for you. If what IT does matters more than what IT is, then...
Are your staff your firm’s biggest security risk?
Well meaning mistakes that could cost you Despite the best technology defenses (next-gen firewalls and antivirus, advanced threat protection, mail washing, web filtering, regular patching) infections and security events can still occur due to what is often the...
Is the organisation doing enough to get the cyber-security cost/risk balance right?
Is your organisation doing enough to get the cyber-security cost/risk balance right? Cyber-security protection can feel like an unending cost.No matter how much you do, there is always more that can be done, and no promises that any of the steps you take will...
Are your staff your biggest security risk?
Despite the best technology defenses (next-gen firewalls and antivirus, advanced threat protection, mail washing, web filtering, regular patching) infections and security events can still occur due to what is often the biggest risk – your staff. Social Engineering...
Do you have an appropriate Data Privacy Policy?
Data privacy is now a hot topic in NZ. This was driven by three main factors: 1. The GDPR (General Data Protection Regulation) which came into effect in Europe in May 2018. This introduced strict regulations on what private information is, how to get consent from...
Do you have the right relationship with your IT provider?
Do you have the right relationship with your IT provider? Regardless of whether your IT provider is your in-house IT team or a trusted business provider, do you have the right relationship with them? The right IT provider will ask "WHY" long before they ask "WHAT" and...



